
212.32.266.234 — What This “IP Address” Really Means
Most times someone looks up 212.32.266.234, it follows an odd event – maybe a firewall flagged activity, strange entries in logs, perhaps chatter online calling that number risky. Reality tends to be less dramatic though. Instead of fixating on a single string of digits, better to see how digital traffic behaves when things run smoothly versus when glitches hit.
From a technical standpoint, this IP address looks suspicious. Though it seems to match the standard IPv4 layout managed by the Internet Protocol, digging deeper shows something is clearly wrong. One basic principle of how IPs are built gets broken here, making it invalid.
Why 212.32.266.234 Is Invalid
IPv4 addresses have four number parts, each of which should be between 0 until 255. The third part here is 266, going over the allowed numbers.
IP Validation Breakdown
| Octet Position | Value | Valid Range | Status |
|---|---|---|---|
| 1st | 212 | 0–255 | Valid |
| 2nd | 32 | 0–255 | Valid |
| 3rd | 266 | 0–255 | Invalid |
| 4th | 234 | 0–255 | Valid |
Because of this, IP 212.32.266.234 does not work as a routable address and is not technically real. It cannot be on the public internet or let it connect to any real network.
What Makes Invalid IPs Important
Even though this IP is invalid, its appearance in logs or alerts should not go unnoticed completely. In cybersecurity, irregularities often transmit meaning outside their face value. Illegal IPs are often indicators of fundamental issues such as bot activity, logging errors, or even deliberate misrepresentation attempts.
Why Invalid IPs Still Appear
| Cause | Explanation | Risk Level |
|---|---|---|
| Log corruption | System errors merge or misread values | Medium |
| Bot traffic | Scripts generate malformed inputs | Medium |
| Attack obfuscation | Hackers inject fake IPs to confuse systems | High |
| Human error | Mistyped or copied incorrectly | Low |
| Viral misinformation | Shared without verification | High |
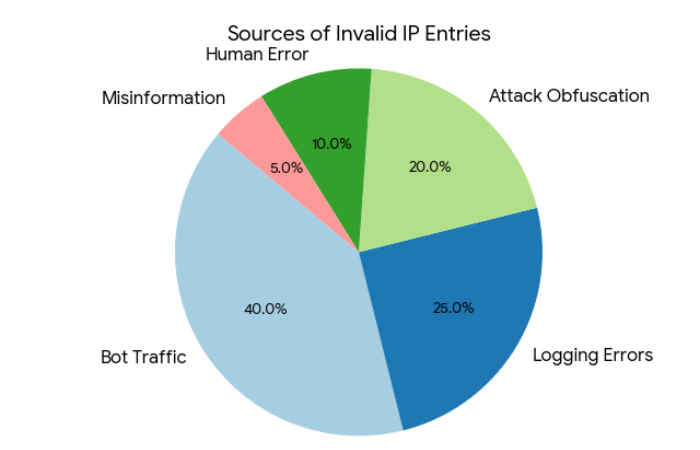
Sources of Invalid IP Entries
How the Internet Treats Invalid IP Addresses
The global internet infrastructure strictly enforces IP formatting rules. Organizations like ICANN and IANA define these standards.
When an invalid IP appears, it is typically rejected before any meaningful routing occurs. Routers and network devices are designed to drop malformed packets instantly.
What Happens Internally
| Step | Process | Outcome |
|---|---|---|
| 1 | Packet received | Checked for structure |
| 2 | IP validation | Fails due to invalid octet |
| 3 | Routing attempt | Not initiated |
| 4 | Packet handling | Dropped silently |
This means the IP cannot directly interact with your system in a legitimate way.
When You See 212.32.266.234 in Logs
Seeing this IP in logs can be confusing, especially for beginners. However, context matters more than the IP itself. It usually appears as part of malformed requests or automated traffic.
Common Log Scenarios
| Scenario | Example | Meaning |
|---|---|---|
| Web server logs | Failed request from IP | Bot or malformed request |
| Firewall alerts | Suspicious traffic entry | Packet anomaly |
| Analytics tools | Visitor IP mismatch | Parsing error |
| Proxy headers | Incorrect forwarding | Misconfiguration |
These entries are often harmless individually but can become significant if they appear repeatedly or in patterns.
How to Analyze Suspicious IP Activity
Reacting with emotion when new IPs appear is not productive and it is much better to use an methodical analysis strategy. This assists to find out if something is just a small issue, or maybe an real risk.
Step-by-Step Analysis Framework
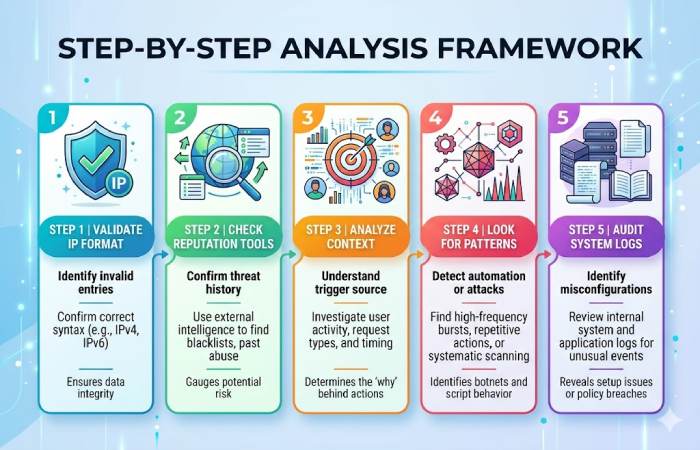
You can use platforms like AbuseIPDB and VirusTotal to verify legitimate IPs—but in this case, the invalid format already answers most questions.
| Step | Action | Purpose |
|---|---|---|
| 1 | Validate IP format | Identify invalid entries |
| 2 | Check reputation tools | Confirm threat history |
| 3 | Analyze context | Understand trigger source |
| 4 | Look for patterns | Detect automation or attacks |
| 5 | Audit system logs | Identify misconfigurations |
Signals vs Noise in Cybersecurity Logs
One of the most important skills in cybersecurity is distinguishing meaningful signals from background noise. Invalid IPs often fall into the “noise” category—but not always.
Signal vs Noise Comparison
| Indicator | Classification | Interpretation |
|---|---|---|
| Single invalid IP | Noise | Ignore |
| Repeated invalid entries | Signal | Possible bot activity |
| Mixed valid/invalid pattern | Signal | Parsing issue |
| Sudden spike | Signal | Attack attempt |
| Random isolated logs | Noise | Normal internet behavior |
Should You Block This IP?
Since 212.32.266.234 is not a valid IP, blocking it specifically has no practical impact. However, the pattern in which it appears may justify broader action.
Recommended Actions
| Situation | Action |
|---|---|
| One-time appearance | Ignore |
| Frequent invalid IPs | Monitor logs |
| Pattern-based anomalies | Apply rate limiting |
| Security-sensitive system | Investigate deeply |
| Large traffic spikes | Enable firewall protections |
Conclusion
212.32.266.234 is actually not valid IP address, but when we see it, it still has meaning.It can show something about the way your systems are working with a wrong or tampered data. This may come from a misconfiguration or bots or even incorrect information, and such irregularities may tell you a lot about operations.
Learning about odd IPs such as 212.32.266.234 make it possible to go from overreacting to thinking with more logic. Instead of only worrying, you can check the context, spot some patterns and decide with the knowledge. In today’s cybersecurity, to switch from panic into a proper analysis is kind of a trait separating people new to the work from specialists.
FAQs
Is 212.32.266.234 real?
No, it’s invalid.
Can it harm my system?
No.
Why does it appear in logs?
Bot traffic or errors.
Should I block it?
Not necessary.
Is it used by hackers?
Sometimes for obfuscation.

